// Blog & News
Cybersec Intel & Research
CVE breakdowns, threat intel, PoC exploits and security research that actually matters.
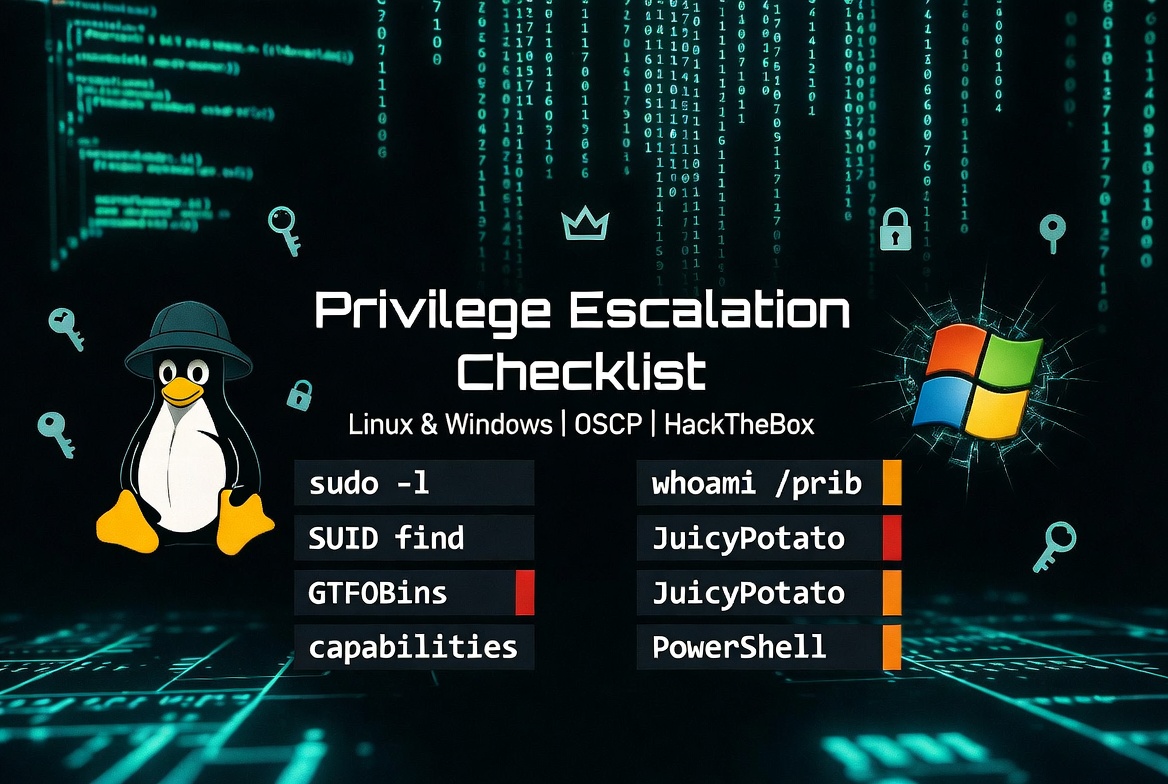
The Privilege Escalation Playbook — Linux & Windows
A practical, command-driven walkthrough for Linux & Windows boxes — HackTheBox / OSCP style. The exact mental model Doomsknight uses on every box, from stable shell to root flag.

CVE-2026-29000: PAC4J JWT Authentication Bypass — Technical Breakdown
A logic flaw in pac4j's JwtAuthenticator allows full authentication bypass by wrapping an unsigned PlainJWT (alg=none) inside a JWE. The server decrypts the envelope, finds a null SignedJWT, skips signature verification entirely, and builds a trusted user profile from attacker-controlled claims.

CVE-2025-9074: Docker Desktop Container Escape — Technical Breakdown
A critical unauthenticated Docker Engine API exposure in Docker Desktop < 4.44.3 allows any Linux container to escape to the host — with full administrative access on Windows. Here's the root cause, full PoC walkthrough, and why ECI did nothing to stop it.
Showing 1–3 of 3 posts